Merge Readiness Explained: Visible, Deterministic, Auditable PR Policy
Code review should be about engineering judgment, not branch protection detective work.
But many teams still end up with pull requests that feel almost ready and yet somehow impossible to merge.
Nobody is fully sure:
which approval is still missing
whether the right team has approved
which check actually matters
whether another pull request is blocking merge
why GitHub still will not allow it
So the conversation shifts away from the code and toward process archaeology:
What is still blocking this?
Is this check required?
Do we need platform review here?
Why is the PR still red?
Is this safe to merge?
That is a poor use of human attention.
Code review is not just bug finding
Good code review is not only about catching defects.
It is also where teams:
share context
align on standards
discuss tradeoffs
spread ownership
mentor newer engineers
improve collective judgment
When merge readiness is unclear, reviewer attention gets pulled away from that higher-value work and into process debugging.
Instead of asking:
Is this design right?
Is the tradeoff acceptable?
Is the risk understood?
Does this align with team conventions?
People ask:
Which check is missing?
Who still needs to approve?
Is this blocked by another policy?
Why is GitHub still not mergeable?
When merge requirements are unclear, review quality suffers because human attention gets spent on process confusion instead of code quality.
The hidden cost of ambiguous merge state
The cost of unclear readiness goes beyond annoyance.
It causes:
pull requests to sit idle longer
authors to guess at the next action
reviewers to waste cycles interpreting state
platform teams to get pinged for explanation
merge confidence to go down
policy enforcement to feel arbitrary
Even when the policy itself is reasonable, poor visibility makes it feel brittle and frustrating.
Often the real issue is not only the rule.
It is the lack of a clear explanation of how the rule applied to this pull request.
Merge decisions should be explainable
For any pull request, a team should be able to answer a few questions immediately:
What approvals are required?
From whom?
What checks are required?
Which ones are complete?
Is a dependency blocking merge?
Which rule caused this requirement?
What exactly remains before merge?
Merge readiness should not have to be inferred from scattered signals across branch protection settings, workflow runs, review threads, labels, and tribal knowledge.
It should be explicitly computed and clearly shown on the PR itself.
A merge decision should read like an explanation, not a puzzle.
Why determinism matters here
Merge decisions should be consistent:
same inputs
same evaluation
same outcome
That matters because teams need:
fairness
predictability
trust
clear expectations
reproducibility in audits and retrospectives
If merge state depends on vague interpretation, different reviewers reach different conclusions, authors get mixed signals, and policy loses credibility.
A merge decision is not just a status.
It is a policy judgment, and policy judgments should be deterministic.
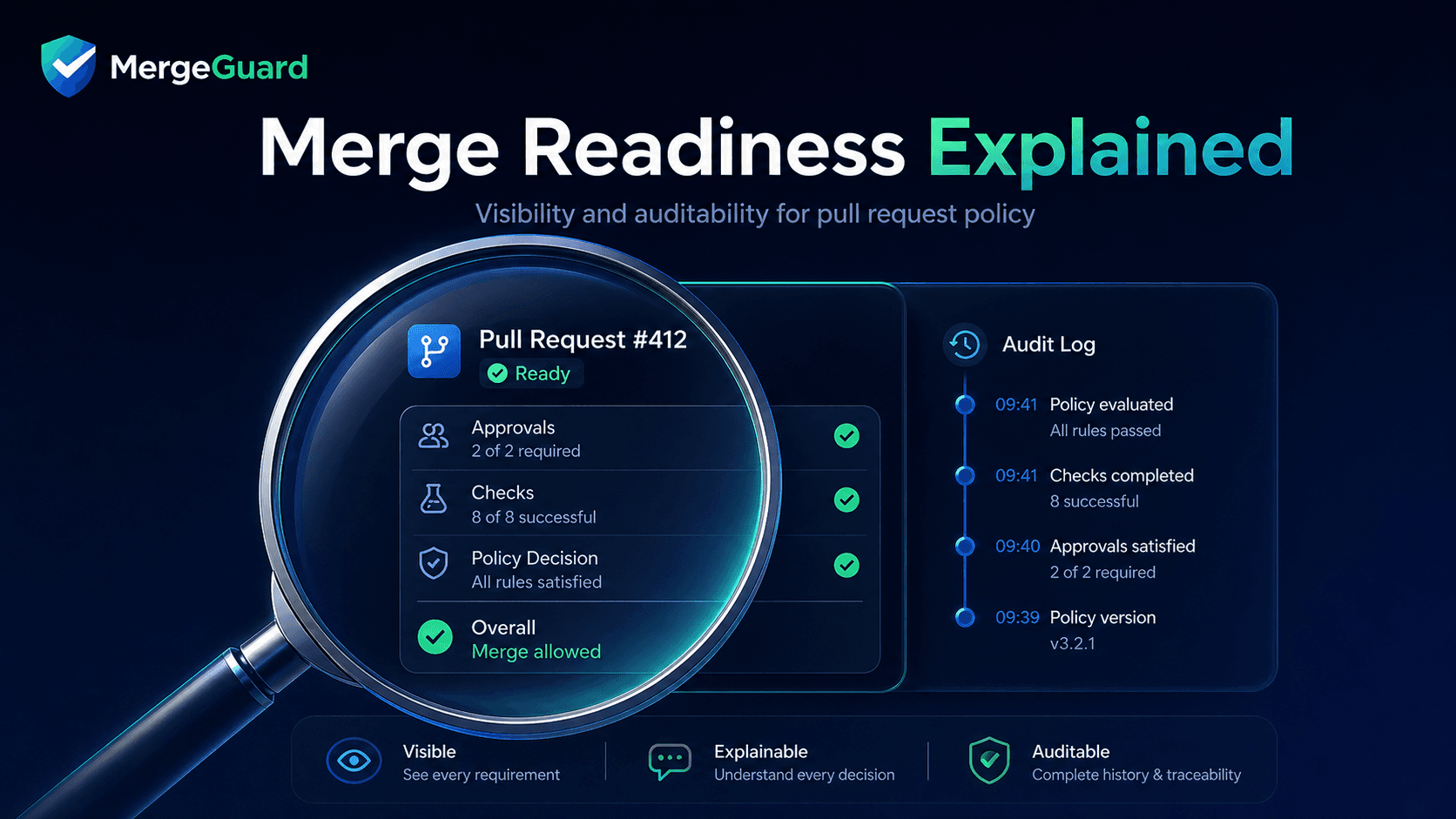
What "merge readiness, explained" looks like in practice
This becomes much easier to understand when the decision is rendered in a readable way.
A strong readiness result can summarize:
required approvals
missing team or user reviews
required checks
pending or failed checks
blocked dependencies
whether merge is allowed
why
For example:
Merge readiness: BLOCKED
Why:
- Platform team approval required because files under infra/ changed
- security-ci required because code under auth/ changed
- PR #123 is a declared dependency and has not merged yet
Current state:
- platform-team approval: missing
- security-ci: pending
- unit-tests: passed
- docs-checks: not required
Next step:
- get platform-team approval
- wait for security-ci to pass
- merge or remove dependency on #123
That is much more useful than a red X with weak context.
Everyone can see:
what the system decided
why it decided it
what to do next
Better for authors, reviewers, and managers
Visible readiness improves flow for several groups at once.
For authors:
the next action is obvious
idle time drops
the real blocker gets fixed faster
For reviewers:
less time is spent interpreting process state
more time goes to design, correctness, and maintainability
it is clearer whether their review is actually required
For managers and platform teams:
fewer interruptions
fewer "why is this blocked?" escalations
clearer policy outcomes
stronger trust in the merge process
Explainability improves flow for everyone, not just compliance teams.
Auditability is not only for regulated companies
Auditability can sound abstract, but the need is common.
Teams often want to answer later:
Why was this PR allowed to merge?
Which approvals were required at the time?
Which checks were considered relevant?
Was an exception used?
Why did this change wait?
Why did a low-risk PR auto-merge?
That matters in ordinary engineering work:
post-incident reviews
team learning
policy tuning
onboarding
understanding historical decisions
A visible merge rationale is useful long before you need formal compliance.
Why native GitHub signals often are not enough
This is not a complaint about GitHub.
GitHub provides valuable raw signals:
checks
reviews
branch protection
mergeability state
The problem is that those signals are often fragmented.
They do not always answer in one clear place:
what is missing
why it is required
whether a dependency is blocking merge
which rule applied
whether a skipped check is actually irrelevant
GitHub shows pieces of the state.
Teams still need a clear decision.
How MergeGuard fits
This is the gap MergeGuard is designed to close.
MergeGuard acts as a deterministic policy layer that evaluates PR context and produces one readable merge readiness result.
It can explain:
which checks matter for this PR
which approvals matter for this PR
whether dependencies block merge
why merge is allowed or blocked
MergeGuard is not just another status.
It is a human-readable policy decision attached to the PR.
Why this improves team behavior, not just tooling
When readiness is explicit:
people trust the process more
reviewers focus on substance
authors move faster
exceptions become more visible
policy conversations become healthier
When readiness is opaque:
people cargo-cult approvals
reviewers rubber-stamp to get green
authors chase ghosts
platform teams become policy interpreters
resentment builds around controls
Explainability improves team dynamics, not just merge mechanics.
Closing
Code review should help teams improve code and judgment together.
That only works well when the merge process itself is clear.
If authors and reviewers have to reverse-engineer readiness from scattered signals, the review process degrades into administrative debugging.
Merge readiness should be:
visible
deterministic
explainable
auditable
And that is exactly the kind of problem MergeGuard is designed to solve.
A pull request should not make you guess what is missing.
MergeGuard gives teams one clear status that explains what is still required for merge: approvals, checks, dependencies, and why.
