AI Can Accelerate Pull Requests — but Merge Still Needs a Deterministic Control Plane
AI Can Accelerate Pull Requests — but Merge Still Needs a Deterministic Control Plane
AI is becoming a useful layer in pull request workflows.
It can generate code, summarize diffs, identify likely ownership areas, explain unfamiliar parts of the codebase, and reduce the amount of raw mechanical work reviewers have to do.
That is not hypothetical value. It is already useful.
But there is a category mistake teams can make when they extend that logic too far.
Helping a pull request move faster is not the same thing as deciding whether that pull request is allowed to merge.
One is assistive.
The other is enforcement.
That distinction matters because merge is where repository governance becomes real.
At merge time, the system is not just offering guidance. It is making a permission decision: does this change satisfy the required conditions to become part of the mainline?
That is not a place where “probably safe” is good enough.
The safest operating model looks like this:
AI suggests and accelerates. Deterministic policy decides and enforces.
Review is probabilistic. Merge should not be.
Code review and merge governance sit next to each other in the workflow, but they solve different problems.
Review is exploratory. It benefits from speed, judgment, context, and pattern recognition. AI is well suited to help there.
Merge governance is different. It is a decision boundary.
At that boundary, the system needs explicit answers to questions such as:
Which domains did this pull request affect?
Which owners are required for those domains?
Which checks must pass for this change type?
Which branch or environment rules apply?
Are any exception paths allowed here?
Is this change currently permitted to merge?
Those are not best-guess questions.
They are policy questions.
And policy questions should be answered deterministically.
For the same inputs, the system should produce the same result every time.
That is what makes a merge decision trustworthy, auditable, and automatable.
Why static repository controls are not enough
GitHub’s primitives are useful and necessary.
Protected branches, required reviews, CODEOWNERS, status checks, auto-merge, and merge queue give teams a solid baseline.
But they are still primitives.
Real governance usually depends on context.
A repository-level rule cannot fully capture the difference between:
a docs-only change
a change under
billing/an infra modification under
infra/a pull request that spans application code, auth config, and deployment changes at once
In real organizations, merge requirements depend on what changed, who owns it, how sensitive it is, and whether the change crosses domain boundaries.
That is why many teams hit the same wall: broad defaults are easy to configure, but precise governance is harder to express.
A concrete failure mode: cross-domain changes with weak enforcement
Consider a pull request that changes:
service logic
Terraform
authentication configuration
The real requirement may be obvious:
service owners should review the service logic
platform owners should review the infrastructure
identity or security owners should review the auth changes
But in many repositories, the merge system cannot directly express “require approval from each affected domain.”
What happens next is predictable:
teams add custom checks
ownership logic gets duplicated in scripts
exceptions are handled manually
engineers learn the “real rules” socially instead of reading them from policy
That is not scalable governance.
That is operational drift.
The core requirement is a policy engine
What scaling teams actually need is not a bigger pile of repository settings.
They need a policy engine.
That policy engine should be able to express rules like:
changes under
infra/require platform approvalchanges under
billing/require billing approvalmulti-domain changes require approval from every affected domain
docs-only changes can follow a lighter merge path
emergency changes can follow a controlled exception path
merge is allowed only when the exact review and check requirements for that change shape are satisfied
These are normal requirements for platform teams and multi-team engineering organizations.
The important part is not just that the rules exist.
It is that they are encoded, explainable, and enforced automatically.
Governance as code is the right abstraction
This is why governance as code is such a useful model.
Instead of distributing merge logic across repository settings, GitHub Actions, ad hoc scripts, and institutional memory, teams can define merge policy from a structured source of truth.
That source of truth can describe:
domains and systems
ownership
approval requirements
sensitivity levels
exception paths
environment-specific policies
From there, the system can derive and enforce the correct merge decision based on the actual shape of the change.
That creates a better control plane for pull request governance.
It also improves auditability. A blocked or approved merge can be explained in terms of policy, not guesswork.
Where AI belongs in this architecture
AI still has an important role.
It can:
summarize large pull requests
identify likely reviewers
point out unusual change patterns
suggest test gaps
help humans understand unfamiliar code paths
That is exactly where probabilistic systems create leverage.
But that layer should remain assistive.
If a model says a pull request “looks safe,” that can be useful reviewer context.
It should not be the mechanism that grants permission to merge.
We already understand this principle in other delivery controls.
Teams do not replace CI with “the model thinks the build is probably okay.”
Merge governance should be treated with the same rigor.
The safer design
The better design is a layered one:
humans provide judgment
AI provides acceleration
deterministic policy provides enforcement
That gives teams the benefits of faster review without turning the merge path into a trust problem.
It also creates clear system boundaries.
AI helps interpret.
Policy decides.
Humans intervene where nuance is genuinely required.
That is a healthier architecture than trying to make a probabilistic assistant the final authority on repository state changes.
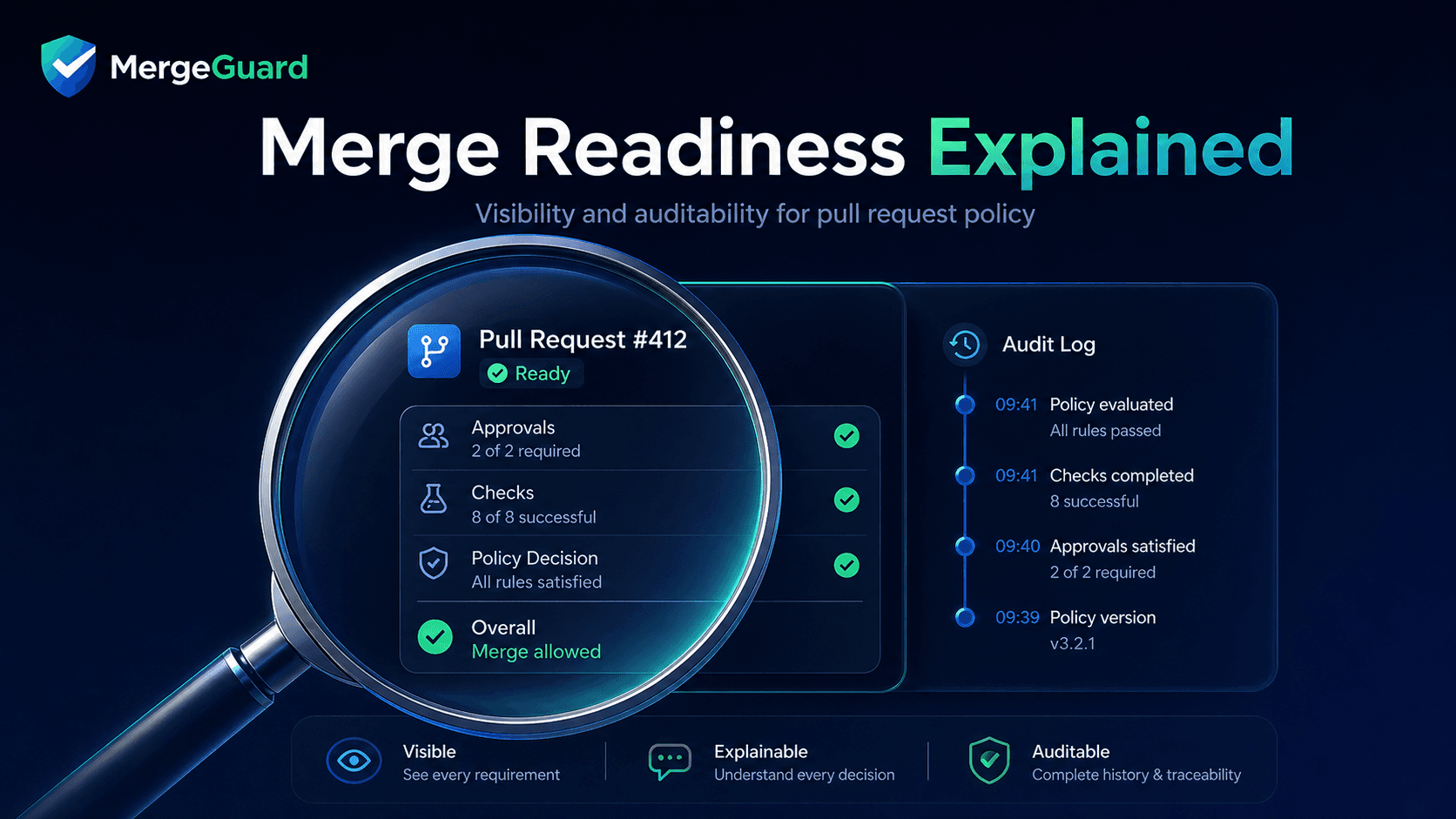
How MergeGuard fits
This is the problem MergeGuard is designed to solve.
MergeGuard adds a deterministic policy layer to GitHub pull request workflows so teams can move beyond one-size-fits-all repository rules and enforce the review logic their systems actually require.
That means merge policy can reflect reality:
which domains were changed
who owns them
which combinations of approvals are required
which exceptions are allowed
when a pull request is truly safe to merge
The goal is not to replace GitHub’s primitives.
It is to turn them into part of a broader, context-aware control plane for merge governance.
That becomes even more important as AI-generated code, agent-created pull requests, and higher-autonomy delivery workflows become more common.
The faster pull requests can be created, the more important deterministic merge enforcement becomes.
Closing
AI should absolutely help teams move faster.
But merge is not just a productivity optimization.
It is a governance boundary.
And governance works best when it is deterministic.
AI should suggest and accelerate. Deterministic policy should decide and enforce.
If your team wants deterministic merge policy for GitHub pull request workflows, learn more at mergeguard.dev.